Nonprofit Cyber Insurance: Guarding Data and Donor Trust
Nonprofits hold some of the most sensitive information in existence-donor details, beneficiary records, financial data. Yet many operate with skeleton IT teams and tight budgets, making them prime targets for cybercriminals.
At Heaton Bennett Insurance, we’ve seen firsthand how a single breach can devastate an organization’s mission and donor relationships. That’s why nonprofit cyber insurance isn’t optional anymore-it’s a business necessity.
Why Cybercriminals Target Nonprofits
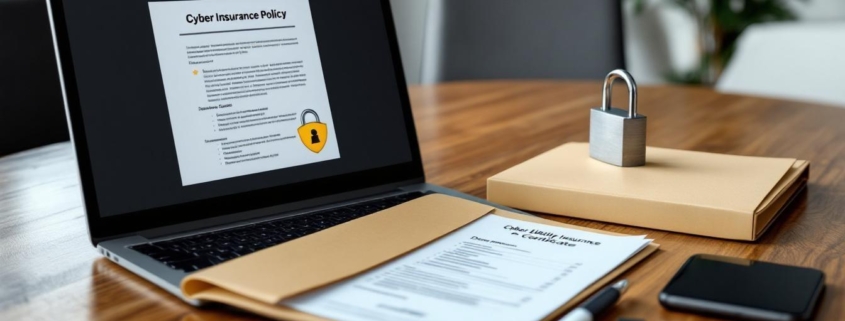
Nonprofits have become high-value targets for cyberattacks, and the reason is straightforward: they hold sensitive data while operating under severe resource constraints. The average cyber claim against nonprofit organizations lands around $98,000, yet most lack the IT infrastructure to defend against modern threats. Unlike corporations with dedicated security teams, nonprofits typically manage their technology with skeleton crews or outsourced consultants who juggle multiple responsibilities. This resource gap isn’t just inconvenient-it’s a critical vulnerability. When your organization processes donor payments, stores volunteer information, and maintains beneficiary records, you manage the exact data criminals want. According to the BBB Wise Giving Alliance’s 2025 Donor Trust Special Report, 28% of donors won’t donate again after a data breach, and 52% pause giving until issues are resolved. That financial impact extends far beyond the breach itself.
The Data You’re Protecting Has Real Market Value
Donor information commands real value on the dark web. Names, addresses, credit card numbers, giving history, and communication preferences create complete identity profiles that criminals can exploit or sell. Your nonprofit isn’t just a charitable organization-it’s a database of personally identifiable information that makes you a target. Ransomware attacks have evolved beyond simple encryption; criminals now exfiltrate data and threaten public release unless you pay. For nonprofits that handle client intake, case management, or grant applications, the exposure multiplies. The challenge intensifies when you outsource functions like payroll processing, bookkeeping, or donation handling. Each vendor connection becomes a potential entry point. About 58% of cyberattacks originate from email inbox compromises, often through phishing that targets staff with access to donor systems. Your team isn’t malicious-they’re just human, and attackers exploit that relentlessly.
Outdated Systems Leave Networks Exposed
Many nonprofits operate on technology purchased five or ten years ago, with software that hasn’t received security patches in months. Legacy systems lack basic protections like multi-factor authentication, which makes password compromise a straightforward path to your entire network. Website vulnerabilities are particularly common; default usernames and weak passwords on content management systems lead to complete site takeovers. When your website gets compromised, cleanup costs mount quickly, and donor trust erodes. The financial impact of ransomware alone averages $172,000 per incident for nonprofits. Add business interruption-the inability to process donations, send communications, or access donor records-and your organization faces operational paralysis precisely when you need to function most.
Recovery Demands External Expertise and Resources
Recovery from a cyberattack requires external forensics experts, breach notification services, and often complete system rebuilds. These costs accumulate fast, and most nonprofits lack the cash reserves to absorb them. Universities, religious organizations, and health charities have all faced significant breaches in recent years, proving that no nonprofit is immune. The question isn’t whether your organization will face a cyber threat-it’s whether you’ll have the financial and operational resources to respond when one strikes. Understanding what coverage you actually need becomes the next critical step.
What Nonprofit Cyber Insurance Actually Covers
Nonprofit cyber insurance isn’t a single product-it’s a collection of protections that address the specific financial fallout from a cyberattack. Understanding what these policies actually cover separates organizations that recover quickly from those that face financial devastation. The average cyber claim against nonprofit organizations sits around $98,000, but the range is enormous. Some incidents cost $50,000; others exceed $1 million. Your coverage needs to match your actual exposure, which means knowing exactly what happens after a breach occurs.
Breach Response and Notification Costs
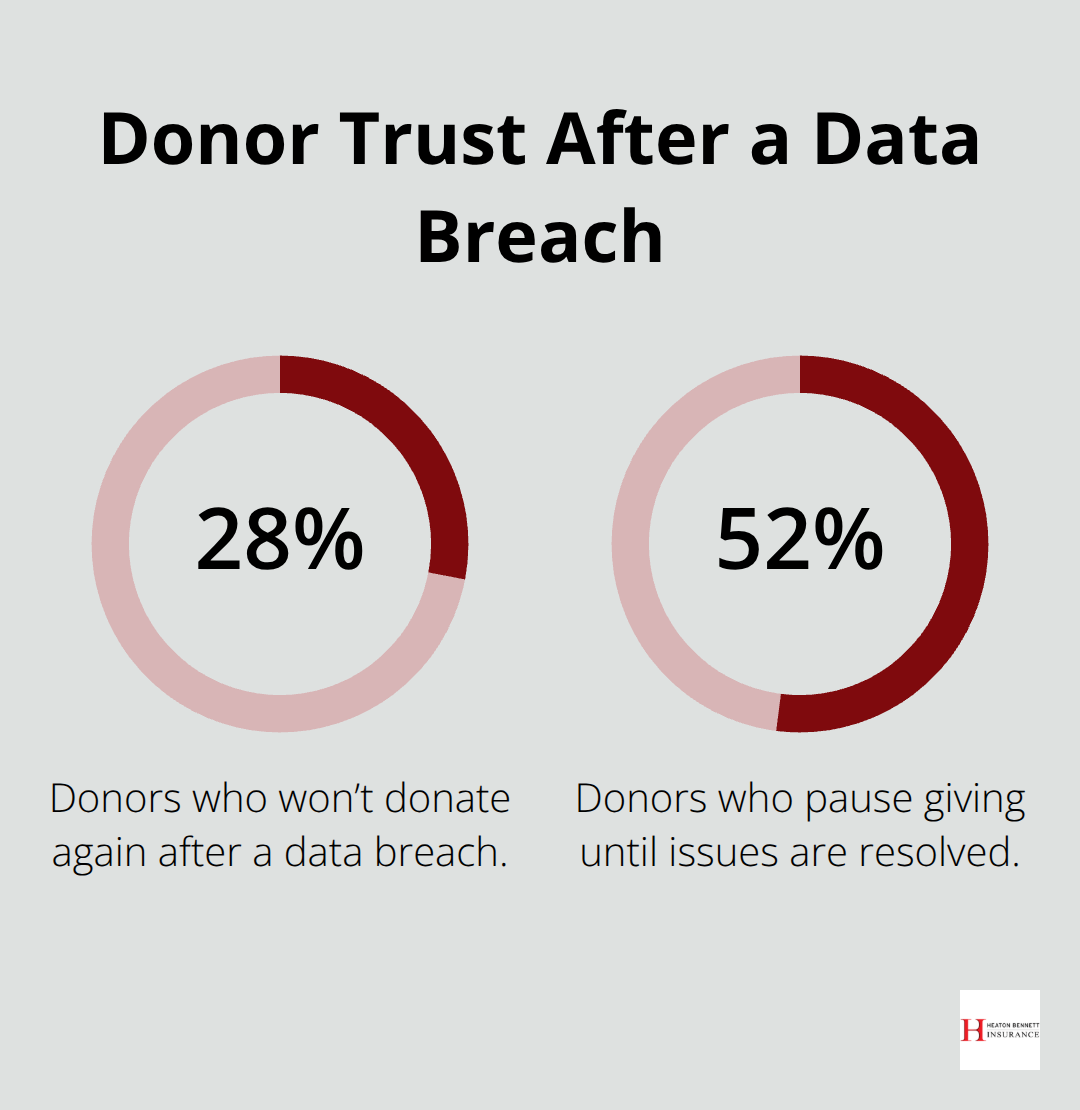
When a data breach happens, your organization faces immediate costs that most nonprofits cannot absorb alone. Breach notification services alone run $10,000 to $50,000 depending on how many people you need to contact. If you’ve stored 50,000 donor records and a breach exposes them, you must notify affected individuals in most states-47 states have mandatory breach notification laws. Specialized vendors handle the logistics, letter writing, and compliance documentation. Credit monitoring services, which many breaches include, add another $5,000 to $20,000. Call centers to handle donor questions after notification can cost $15,000 to $40,000. Forensic investigation to determine what happened and how attackers got in typically runs $30,000 to $100,000 depending on complexity. These aren’t optional expenses-they’re legal and practical necessities.
Without cyber insurance, your organization pays these costs directly from reserves or operating budgets, immediately crippling your ability to serve your mission. A solid cyber policy covers all of these breach response expenses, meaning your organization focuses on recovery rather than financial crisis. Your policy should also cover regulatory fines and penalties. If your nonprofit handles data on EU citizens, GDPR violations can result in substantial fines. Even without international exposure, state privacy laws are multiplying-at least 20 states now have consumer data privacy laws-and noncompliance carries financial penalties.
Business Interruption and Operational Recovery
Business interruption coverage addresses what happens when your systems go offline. If ransomware encrypts your donor database or a DDoS attack takes down your website, you cannot process donations, send communications, or access critical records. For many nonprofits, even three days of downtime represents thousands in lost revenue. Ransomware attacks against nonprofits average $172,000 in losses. Business interruption coverage reimburses lost revenue during the outage period, typically covering 30 to 90 days depending on your policy.
Some policies also include dependent business interruption coverage, which protects you if your vendor-your payment processor, email provider, or cloud storage company-gets attacked and their outage disrupts your operations. This matters because IT supply chain attacks are rising, and your nonprofit cannot control whether your vendors get breached. Your organization remains vulnerable to vendor failures even when your own systems are secure.
Ransomware, Extortion, and Reputation Management
Ransomware and extortion coverage directly addresses the reality that criminals now steal data before encrypting systems. They threaten to publicly release donor information unless you pay. Your policy should cover ransom payments if you choose to pay them, though law enforcement generally discourages this. More importantly, extortion coverage includes the costs of negotiating with attackers, hiring breach counsel to coordinate response while maintaining attorney-client privilege, and managing the threat of data release.
It also covers public relations expenses to manage your reputation if stolen data does get released. The reputational damage from a data breach can persist for up to four years according to research by Christoph Schiller, meaning your organization needs resources to actively rebuild trust with donors and the public. Coverage should include crisis communications support to craft messages that acknowledge what happened, explain what you’re doing to fix it, and demonstrate commitment to protecting data going forward.
Rapid Access to Vetted Response Vendors
Look for policies that include access to pre-vetted breach response vendors. When an incident happens, you don’t have time to shop for forensics firms or notification services. Insurers maintain panels of vetted vendors who understand nonprofit operations and can mobilize quickly. This vendor network dramatically accelerates recovery and reduces the friction of coordinating response during the chaos of an active incident. The difference between having immediate access to trusted vendors versus scrambling to find competent help can mean days or weeks of additional downtime-time your organization cannot afford to lose.
With the right coverage in place, your nonprofit transforms from a vulnerable target into an organization prepared to respond. The next step involves building the security foundation that works alongside your insurance to actually prevent attacks from succeeding in the first place.
Securing Access Before Attackers Find a Way In
Control Who Reaches Your Data
Insurance covers the financial damage, but preventing breaches demands operational discipline. Your nonprofit must implement controls that make attacks costly and time-consuming enough that criminals move on to easier targets. The foundation starts with access management, which determines who can reach your donor data and when. Many nonprofits grant broad access permissions during onboarding and never revisit them. A staff member leaves, a volunteer’s role changes, or a contractor finishes their project-yet their access remains active indefinitely. This violates the principle of least privilege, meaning each person should have access only to data and systems necessary for their specific role.
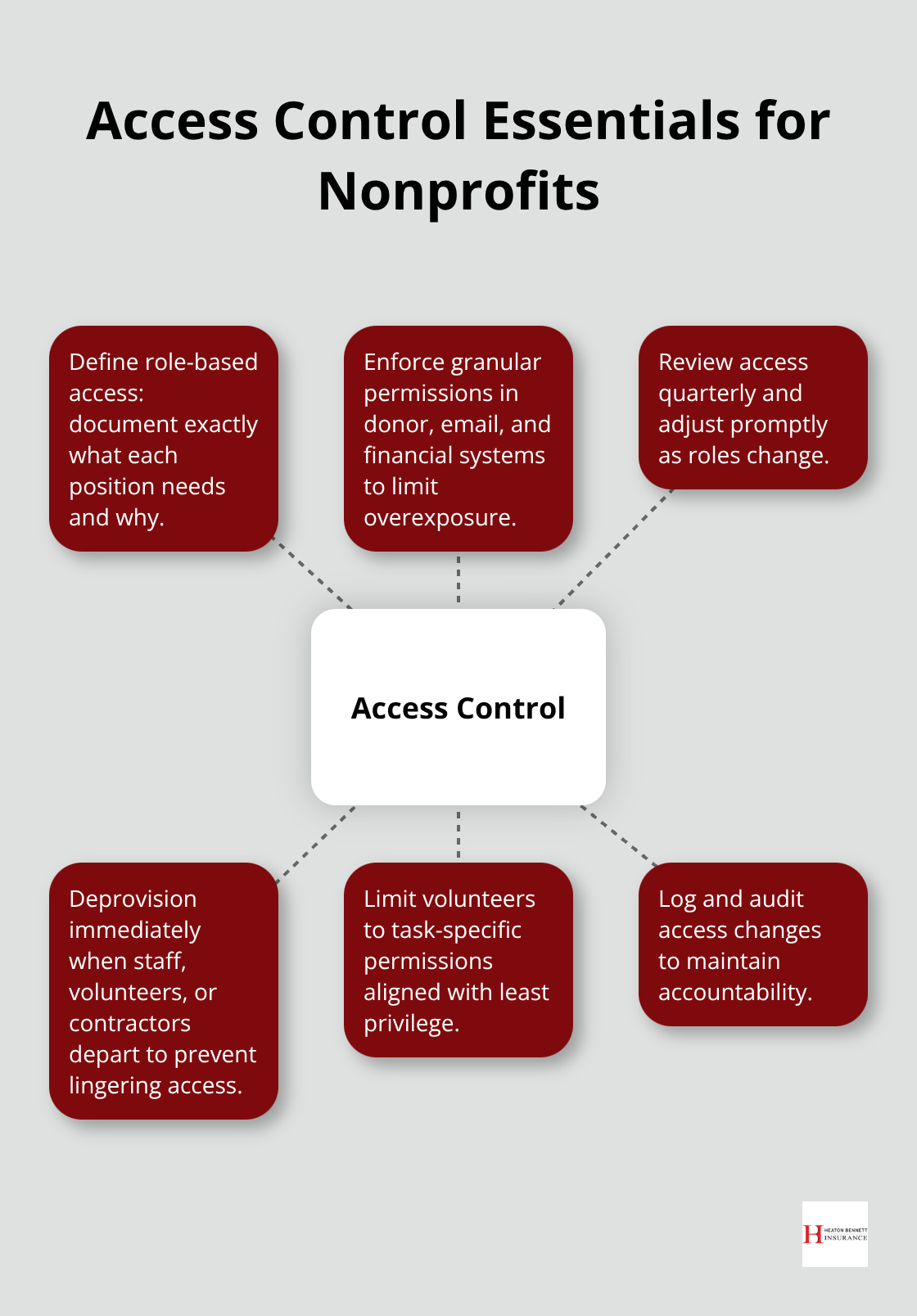
Document what each position actually needs. Your finance director needs access to donation records and bank accounts, but your communications coordinator doesn’t. Your executive director needs broad access, but a data entry volunteer needs only the ability to input new donor information into a single form. Once you define these roles, enforce them through your donor management system, email, and financial software. Most platforms allow granular permissions-use them. Review access quarterly and disable accounts for staff who have left or changed roles.
Require Multi-Factor Authentication for All Data Access
Multi-factor authentication adds a second verification step beyond passwords, requiring users to confirm their identity through a phone app, text message, or hardware key. About 58% of cyberattacks originate from email inbox compromises, and multi-factor authentication stops attackers cold even when they’ve obtained valid passwords. This is non-negotiable for anyone accessing donor data, financial systems, or administrative functions. The setup takes 30 minutes per person, and the protection justifies the minor inconvenience. Attackers may crack a password, but they cannot access your systems without the second factor in hand.
Train Staff to Recognize and Resist Phishing
Staff training directly addresses the human vulnerability that criminals exploit relentlessly. Phishing emails that impersonate donors, vendors, or board members land in inboxes daily, and untrained staff click malicious links or download infected attachments without hesitation. Your nonprofit needs mandatory cybersecurity training when staff are hired and annual refresher training thereafter. The training should cover specific threats: how to spot phishing attempts, why strong passwords matter, how to handle sensitive data, and what to do if they suspect a breach. Real-world examples from nonprofit breaches make training memorable and relevant. The University of Pennsylvania experienced a significant breach through compromised email accounts, demonstrating that prestigious institutions face the same risks as smaller nonprofits.
Training should also address vendor risk, since outsourced bookkeepers, IT consultants, and payment processors access your data. Before engaging any vendor, require documentation of their security practices and data protection agreements. Ask specific questions: Do they encrypt data in transit and at rest? How often do they conduct security audits? What happens if they experience a breach? These conversations identify vendors who take security seriously and eliminate those who don’t.
Test Your Defenses Before Criminals Do
Vulnerability assessments and penetration testing identify weaknesses before attackers exploit them. A vulnerability assessment scans your systems for known security flaws-unpatched software, default passwords, missing encryption. Penetration testing goes further, with qualified professionals attempting to break into your systems using the same techniques criminals employ. Both services typically cost $2,000 to $10,000 depending on your organization’s size and complexity, but they reveal specific gaps you can address. Many cyber insurance carriers offer discounted or free vulnerability assessments as part of policy benefits, making this an opportunity to strengthen your security posture while reducing your insurance risk profile. The assessment results provide a roadmap for prioritizing security investments and closing the most dangerous vulnerabilities first.
Final Thoughts
Your nonprofit’s mission depends on donor trust, and donor trust depends on protecting the data people entrust to your organization. Nonprofit cyber insurance combines financial protection with operational safeguards, covering the costs that would otherwise devastate your budget when a breach happens. When prevention works, your security controls stop attackers before they cause damage.
Cybersecurity requires investment, but the cost of inaction far exceeds the cost of protection. A single breach costs your nonprofit $98,000 on average, damages donor relationships for years, and diverts resources from your mission. Strong security actually strengthens your mission by preserving donor trust and operational continuity.
Start by assessing what data your nonprofit holds, who has access to it, and what would happen if that data got stolen or your systems went offline. Then implement the controls that matter most: multi-factor authentication, staff training, and vendor vetting. Finally, contact Heaton Bennett Insurance to secure nonprofit cyber insurance coverage that matches your actual exposure and protects the donors who make your work possible.
The information provided in this blog is for general informational purposes only and does not constitute legal, financial, or insurance advice. Coverage options, terms, and availability may vary. Please consult with a licensed professional for advice specific to your situation.